Xona Fortifies Critical Infrastructure With Resilient Remote Access
- Nearly half of all industrial control system (ICS) incidents originated from internet-accessible devices and remote services (SANS Institute, 2024).
- NERC CIP-003-9 mandates strict controls on vendor electronic remote access, enforced from April 2026.
- Xona Platform v5.5 introduces Session Hold and RDP Auto-Reconnect for uninterrupted remote access in unstable OT environments.
Experts agree that Xona's Platform v5.5 addresses critical gaps in OT security by combining session resilience with centralized governance, aligning with Zero Trust principles and regulatory mandates like NERC CIP and IEC 62443.
Xona Fortifies Critical Infrastructure With Resilient Remote Access
HANOVER, Md. – February 23, 2026 – As operators of the world’s most essential services face a perfect storm of sophisticated cyber threats and tightening regulations, Xona Systems today announced the launch of its Platform v5.5. The new secure access solution is purpose-built to address the harsh operational realities of critical infrastructure, offering session resilience and centralized governance that legacy tools like VPNs were never designed to provide.
The announcement comes at a pivotal moment for industrial security. Remote access paths remain a primary vector for attacks on operational technology (OT), a fact underscored by industry research. The SANS Institute's 2024 cybersecurity report found that nearly half of all industrial control system (ICS) incidents originated from internet-accessible devices and remote services, highlighting a critical vulnerability in the systems that manage power grids, water treatment facilities, and manufacturing plants.
Navigating the Regulatory and Threat Gauntlet
Critical infrastructure operators are no longer just defending against opportunistic hackers; they are on the front lines of a digital battlefield against well-funded, nation-state-backed threat actors. These adversaries specifically target OT and ICS environments, seeking to disrupt essential services. This heightened threat environment has been met with a wave of stringent regulatory mandates demanding demonstrable proof of security and control.
Frameworks like the North American Electric Reliability Corporation's Critical Infrastructure Protection (NERC CIP) standards, the international IEC 62443 series, and the Transportation Security Administration's Security Directive 2 (TSA SD2) for pipelines have become the law of the land. These regulations require granular access controls, multi-factor authentication, comprehensive logging, and the ability to audit every remote connection. For example, recent NERC CIP updates like CIP-005-7 mandate multi-factor authentication for all remote logins, while CIP-003-9, set to be enforced from April 2026, imposes strict controls on vendor electronic remote access.
These rules, alongside guidance from the National Institute of Standards and Technology (NIST) that increasingly incorporates Zero Trust principles, are pushing organizations to abandon outdated security models. Traditional IT tools like VPNs and jump servers, which often provide broad, high-trust access, are proving insufficient for the segmented, high-stakes world of OT, creating a significant compliance and security gap that solutions like Xona's aim to fill.
Access That Survives Reality
A core innovation in Xona Platform v5.5 is its focus on session resilience, a direct response to the challenging conditions where critical infrastructure operates. Unlike corporate offices with stable, high-bandwidth internet, OT environments are often located on offshore platforms with intermittent satellite links, in rural substations with constrained bandwidth, or within air-gapped industrial facilities.
In these settings, a momentary network disruption can cause traditional remote sessions to crash, forcing operators to restart complex procedures and re-authenticate, wasting valuable time during critical maintenance or incident response. This frustration often leads to a dangerous disconnect between security policy and operational reality, incentivizing staff to find insecure workarounds to get the job done.
Xona’s new platform introduces Session Hold and RDP Auto-Reconnect capabilities to solve this problem. These features are designed to preserve the state of a user's session through network interruptions. If a connection drops, the platform holds the session securely on its gateway. When connectivity is restored, the operator can resume their work seamlessly, without losing progress or needing to log in again. This is achieved within a secure proxy architecture that shields the underlying OT asset from direct exposure, ensuring that resilience does not come at the cost of an expanded attack surface.
"In critical infrastructure, remote access is no longer just about getting connected, it's about maintaining control under pressure," said Raed Albuliwi, Chief Product Officer at Xona, in the company's announcement. "Access models that only work when networks are stable or environments are simple don't hold up in critical infrastructure. Operators need governance that holds up in the field, not just on paper."
Unified Governance Across a Distributed World
Beyond individual session stability, Xona Platform v5.5 enhances its Xona Centralizer to provide a true single-pane-of-glass for managing secure access across a global enterprise. For large utilities or manufacturers with dozens or hundreds of sites, managing access on a location-by-location basis is an administrative nightmare that creates inconsistent security policies and blind spots.
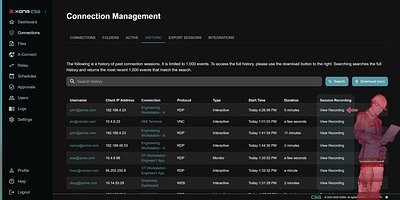
The platform enables security teams to centrally manage connection structures, security policies, and user permissions, and enforce them across all connected gateways. It also centralizes the collection of session recordings, logs, and bandwidth metrics, providing an authoritative, audit-ready trail of every action taken. This is crucial for demonstrating compliance with regulations like NERC CIP and IEC 62443.
This centralized model ensures that even when a remote site has unstable connectivity, the security and access policies remain enforced. The platform also features integrations with other major OT security platforms from partners like Forescout and Nozomi Networks, allowing organizations to build a cohesive security ecosystem where asset visibility informs access control policy.
This purpose-built approach is gaining traction in a competitive market that includes both broad cybersecurity giants adapting IT products and other specialized OT security firms. Xona’s focus on the specific operational pain points of industrial environments appears to be a key differentiator.
"Xona's centralized control, policy enforcement, and audit trail capabilities make it an ideal complement to our OT cybersecurity offering," noted Iain Slater at Barrier Networks, a managed security service partner. "Our clients need secure access that aligns with zero trust and is built for operational realities. Xona delivers that."
With deployments in over 40 countries across the energy, manufacturing, and maritime sectors, Xona is positioning its platform not merely as a tool for connection, but as a foundational element of governance and operational resilience. For industries where uptime is paramount and security failures can have catastrophic consequences, this shift from access that simply connects to access that governs and survives may prove to be a critical evolution.
