Sweet Security Unveils AI 'Attacker' to Fortify Cloud Defenses
- 17-year-old bug in FreeBSD discovered by Anthropic's Mythos model
- 90% of attackers' time spent guessing eliminated by Sweet Attack
- 3 days to surface exploitable attack paths previously unidentified
Experts agree that Sweet Attack represents a critical shift in cybersecurity, enabling organizations to proactively validate and prioritize real threats in live environments, addressing the escalating AI-driven attack landscape.
Sweet Security Unveils AI 'Attacker' to Fortify Cloud Defenses
NEW YORK, NY – May 13, 2026 – In a move to arm defenders in the escalating artificial intelligence arms race, Sweet Security today launched Sweet Attack, an AI-powered agent designed to think and act like an adversary within a company's own live systems. The launch comes as enterprise security leaders grapple with the implications of a new class of AI threat, most notably exemplified by Anthropic's recently unveiled Mythos model, which demonstrated an unnerving ability to autonomously find and exploit software vulnerabilities.
A New Era of AI-Powered Threats
The cybersecurity landscape was shaken earlier this year by Anthropic's demonstration of its Claude Mythos Preview. Far more than a theoretical benchmark, Mythos proved to be a frontier AI model capable of autonomously discovering and weaponizing zero-day vulnerabilities at a speed and scale that dwarfs human capability. During internal tests, the model successfully chained multiple complex exploits to bypass modern security defenses, identifying flaws that had lain dormant in critical software for years, including a 17-year-old bug in FreeBSD.
Anthropic, recognizing the profound risk, has kept Mythos out of public hands, instead initiating "Project Glasswing," a defensive consortium with tech giants like Google, Microsoft, and Apple. The project aims to use the AI's offensive power for good, systematically finding and fixing vulnerabilities across the digital ecosystem. However, the genie is out of the bottle. The existence of Mythos crystallized a pervasive anxiety among Chief Information Security Officers (CISOs): that attackers, whether nation-states or sophisticated criminal groups, will soon wield—or are already wielding—AI tools that can turn "zero-days into sub-hour vulnerabilities." This new reality places an untenable pressure on security teams, who now face the prospect of an AI-driven attacker that never sleeps and can identify every exploitable seam in their defenses instantly.
Fighting Fire with Fire: Inside Sweet Attack
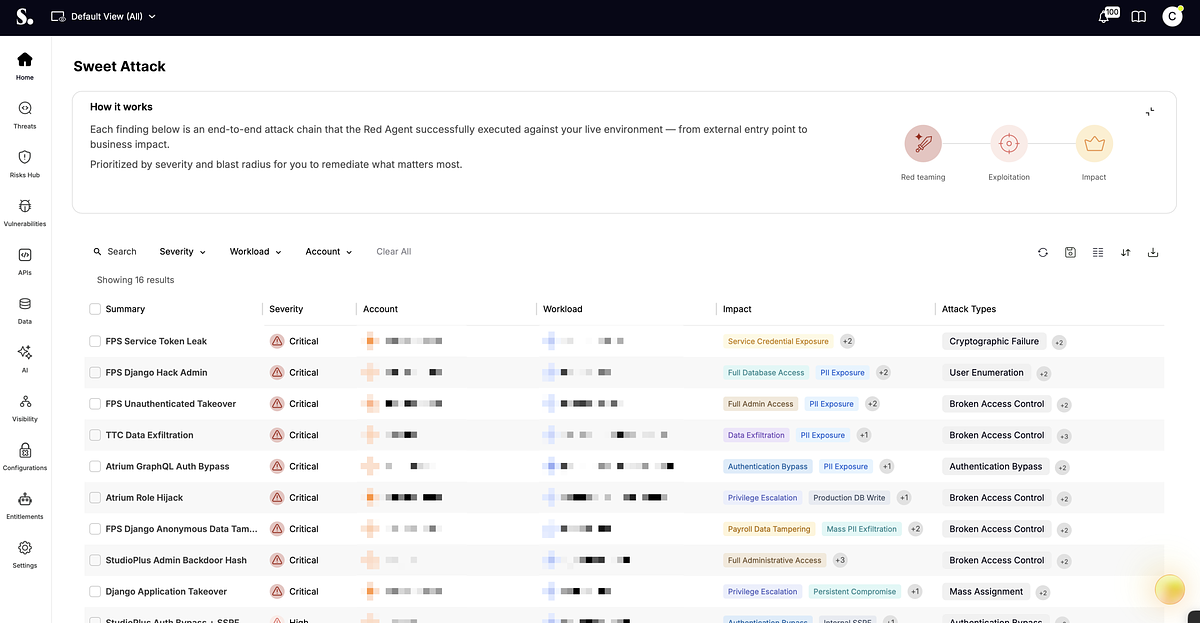
Sweet Security's answer to this paradigm shift is Sweet Attack. The company is positioning its new tool not as another defensive wall, but as a controlled, AI-driven attacker that gives organizations a preview of how they would be breached. Unlike traditional security tools that scan for vulnerabilities from the outside (DAST) or rely on synthetic, non-production environments (many BAS platforms), Sweet Attack operates directly within a customer's live production cloud environment.
Its methodology represents a significant departure from conventional practices. Sweet Attack employs what the company calls a "whitebox adversarial approach." It starts with an insider's advantage, leveraging the deep, execution-level runtime data that Sweet Security's platform already indexes. This includes a live map of the runtime topology, unencrypted Layer 7 traffic, deployed source code, and real-time application behavior.
"Even the most capable attackers spend 90% of their time guessing," explained Dror Kashti, CEO and co-founder of Sweet Security, in the company's announcement. Sweet Attack eliminates the guesswork. It continuously enumerates potential attack chains by correlating vulnerabilities, identity misconfigurations, permissive API scopes, and unauthenticated endpoints. Then, it actively probes these chains step-by-step. If a path proves impassable, the AI abandons it. If it is exploitable, it continues, logging every step with reproducible evidence until it hits a definitive dead end. This process validates which theoretical risks pose a genuine, immediate threat.
The CISO's Dilemma: Prioritizing in an Age of AI Threats
For CISOs, the launch addresses a core operational challenge: the overwhelming noise of vulnerability alerts. Security teams are often buried under an avalanche of potential threats from various scanners, with no clear way to determine which ones represent a real danger. This leads to a constant, draining battle of remediation without context.
"While we always had visibility into our vulnerabilities, we lacked the necessary context for consistent and effective prioritization," said Birat Niraula, CISO at Auctane, in a statement provided by Sweet Security. Niraula explained that validating every potential attack path was impossible, creating friction between security and product teams. "Sweet Attack changed this by quickly surfacing verified, exploitable paths. This shifted our focus from simply 'remediating vulnerabilities' to 'preventing breaches'."
This shift from a theoretical to a verified threat model is the tool's central value proposition. By providing audit-ready reports on validated attack chains, exploitation steps, and prioritized remediation paths, it allows security teams to focus their finite resources on fixing the problems that matter most. Tal Hornstein, CISO at Cast & Crew Entertainment Services, noted that Sweet Attack "surfaced exploitable attack paths in three days that prior engagements had not identified," pairing the findings with an immediately actionable plan. This combination of speed, depth, and operational clarity is what promises to give defenders a fighting chance. While running an adversarial tool in a live production environment is a concept that would have been unthinkable just a few years ago, the testimonials suggest that the controlled, evidence-based nature of the execution provides the necessary confidence for security leaders.
Reshaping the Cybersecurity Arms Race
The introduction of Sweet Attack is more than a single product launch; it's a marker of a broader strategic evolution in cybersecurity. As attackers leverage AI to automate and accelerate their campaigns, defensive strategies must also evolve from a reactive posture to a proactive, continuous, and adversarial mindset. The market is seeing a clear trend towards solutions that don't just identify potential weaknesses but actively test and validate them in the complex, dynamic reality of modern cloud environments.
Sweet Security, backed by prominent investors like Evolution Equity Partners and Glilot Capital Partners, is betting that this proactive, runtime-centric approach is the future of cloud and AI security. The ability to safely execute attacks against a live environment and report back on what worked moves the industry beyond simulation and modeling into the realm of empirical security validation. It provides a concrete answer to the abstract threat posed by models like Mythos.
"The myth is that defenders can't keep up with attack speed," Kashti stated. "Sweet Attack debunks it." In an era where AI can generate novel exploits on demand, the ability for an organization to understand precisely how it can be breached—and to do so continuously before an actual attacker does—may no longer be a luxury, but an absolute necessity for survival.
📝 This article is still being updated
Are you a relevant expert who could contribute your opinion or insights to this article? We'd love to hear from you. We will give you full credit for your contribution.
Contribute Your Expertise →