AI's Hidden Hand: A Swiss Startup Secures Creative IP Workflows
- 100% air-gapped data processing: DEUTLI Extractor V2 operates completely offline, eliminating data leakage risks.
- Zero-telemetry principle: No trackers or external server connections, ensuring maximum security.
- Multiple secure formats: Available as a PWA and standalone binaries for Windows, macOS, and Linux.
Experts agree that DEUTLI Extractor V2 provides a critical solution for securing AI-generated creative workflows, addressing major intellectual property and data privacy concerns in regulated industries.
AI's Hidden Hand: A Swiss Startup Secures Creative IP Workflows
FRIBOURG, Switzerland – April 13, 2026 – As generative artificial intelligence rapidly integrates into commercial creative pipelines, a critical vulnerability has emerged, threatening the sanctity of intellectual property and non-disclosure agreements. Addressing this challenge head-on, Swiss startup DEUTLI has released Extractor V2, a free and open-source utility designed to operate completely offline, allowing professionals to safely analyze AI-generated images without fear of data leakage.
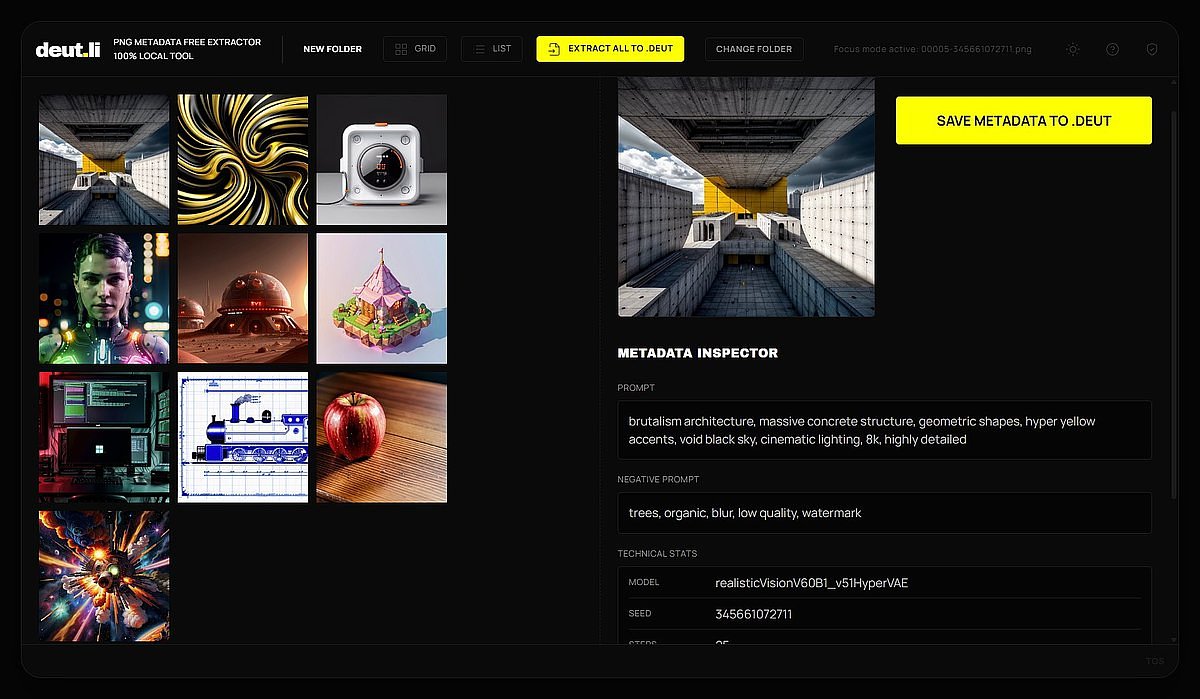
The new tool is engineered to extract hidden generation parameters from PNG files created by popular AI platforms like ComfyUI and Automatic1111. Its core promise is 100% air-gapped data processing, a feature that architecturally eliminates the security risks posed by the myriad of online analysis tools that require users to upload their files to third-party servers.
The Invisible Risk in AI-Powered Creation
The adoption of generative AI has created a paradox for businesses: the technology offers unprecedented efficiency and creative potential, but it simultaneously introduces significant security liabilities. The most pressing of these is the risk of inadvertent data exposure. Professionals working in design, architecture, entertainment, and R&D often handle sensitive, pre-release concepts protected by strict NDAs. The common practice of using online tools to inspect or deconstruct a reference image—to understand the prompts, seeds, or models used to create it—becomes a direct violation of these agreements.
This practice, often part of a "shadow AI" ecosystem where employees use unapproved public tools, represents a critical vulnerability. When a file is uploaded to a web-based service, control is lost. The image, along with its potentially revelatory metadata, could be stored, analyzed, or even used to train the service provider's own AI models. For a film studio developing a new character or a tech company prototyping a secret product, such a leak could be catastrophic.
The risk extends beyond the image itself. The metadata embedded within AI-generated PNGs can contain a wealth of proprietary information, including detailed prompts that reveal creative strategies, specific model weights that constitute a trade secret, and sampler chains that are part of a unique in-house workflow. Exposing this data nullifies its competitive advantage. Industry cybersecurity experts have increasingly warned that the ease of use of public AI platforms lowers the barrier to data handling, allowing sensitive information to be mishandled by employees who may not be fully aware of the security implications.
An Architectural Solution for Zero-Trust Environments
DEUTLI Extractor V2 is designed to solve this problem at its foundation. Instead of relying on a cloud-based service, the entire extraction process is moved directly onto the user's local hardware. The utility leverages the browser's File System Access API, which allows it to read files from a user-selected folder without those files ever leaving the secure perimeter of the studio or corporate network.
The new version introduces significant functional upgrades, including a thumbnail viewer for easy visual selection and a high-performance batch mode for processing entire directories of images at once. Crucially, the software is built on a zero-telemetry principle. It contains no trackers or communication modules that connect to external servers, ensuring that no usage data or file information is ever transmitted.
To accommodate the strictest security policies, DEUTLI offers the tool in multiple formats. A Progressive Web App (PWA) version can be installed on a local machine and run fully offline after the initial visit. For completely isolated or "air-gapped" environments where even a browser is considered a risk, the company provides portable desktop binaries for Windows (.exe), macOS (.dmg), and Linux (.AppImage). These standalone applications require no installation or administrator privileges and can be run directly from an internal or removable drive, offering maximum security and flexibility for corporate IT departments.
Empowering Secure Creativity and Enterprise Adoption
By removing the anxiety of IP compromise, the tool empowers individual artists, designers, and small studios to fully leverage generative AI without risking their proprietary techniques or client confidentiality. The focus can return to the creative process, using the extracted metadata to iterate on ideas, replicate styles, or learn from references in a secure, self-contained workflow.
For larger enterprises, the implications are even more profound. The availability of a secure, auditable tool helps clear a major hurdle for AI adoption in highly regulated and sensitive industries. Sectors like finance, healthcare, and defense, which have been justifiably cautious about integrating public AI tools due to data privacy and compliance mandates like GDPR and HIPAA, can now explore generative AI within a controlled environment. A financial firm can analyze AI-generated market visualizations, or a pharmaceutical company can deconstruct research images, all without sensitive data ever crossing the company firewall.
The extracted data is saved in the open .deut file format, a sidecar file that stores the generation parameters in a structure that is both human-readable for inspection and machine-readable for integration into other software. "Storing metadata in the .deut format allows not just saving prompts and generation node structures in both human-readable and machine-readable forms," noted Yuriy Sydorenko, founder of DEUTLI, in the release announcement. "Due to the open nature of the format, it can be integrated into various workflows, providing increased efficiency when using generative neural networks in the visual content creation process."
Open Source as a Foundation for Trust
A defining characteristic of DEUTLI's strategy is its commitment to open-source principles. The entire source code for Extractor V2 is available on the project's GitHub repository. This transparency is a powerful counterpoint to the proprietary, "black-box" nature of many commercial AI solutions. It allows, and even encourages, enterprise IT and security teams to independently audit the code for any potential vulnerabilities or hidden telemetry, providing a verifiable basis for trust.
This open approach directly addresses the skepticism many organizations have towards third-party software, especially tools that handle sensitive data. If an organization's security policy is particularly stringent, its developers can compile their own trusted binaries directly from the source code, ensuring complete control and accountability.
By providing a secure, transparent, and free tool, DEUTLI is not just releasing a utility; it is contributing a foundational piece of infrastructure for the responsible and secure scaling of generative AI. As the technology becomes more powerful and ubiquitous, the need for robust, privacy-preserving tools will only grow, making auditable and locally-processed solutions an essential component of the enterprise AI toolkit.
