Operation Alice: AI Cracks Vast Dark Web Child Abuse Scam Network
- 373,000 micro-shops: The network consisted of 373,000 individual onion domains on the dark web.
- EUR 345,000 (USD 400,000): The operator amassed this amount in cryptocurrency between 2020 and 2025.
- 600 users investigated: Authorities are pursuing approximately 600 users worldwide who attempted to purchase illegal content.
Experts agree that Operation Alice represents a significant advancement in combating dark web criminality, demonstrating how AI and data-driven tools can dismantle even the most fragmented and anonymized networks, while also highlighting the importance of global law enforcement cooperation.
Operation Alice: How AI Dismantled a Vast Dark Web Abuse Network
THE HAGUE, Netherlands – March 20, 2026 – An unprecedented international law enforcement effort, dubbed 'Operation Alice', has successfully dismantled one of the largest fraudulent networks ever discovered on the dark web, a sprawling empire of over 373,000 "micro-shops" advertising child sexual abuse material (CSAM) and other cybercrime services. The operation, coordinated by Germany's Bavarian Central Office for the Prosecution of Cybercrime (ZCB), culminated in the seizure of the entire network and the issuance of an international arrest warrant for its sole operator.
The breakthrough was made possible by cutting-edge analytical technology from The Hague-based firm CFLW Cyber Strategies, which allowed investigators to piece together a puzzle that spanned nearly half the dark web. This case marks a significant evolution in the fight against online criminality, demonstrating that even highly fragmented and anonymized criminal enterprises are vulnerable to data-driven investigation.
A Web of Deceit: The 'Micro-Shop' Empire
At the heart of Operation Alice was a sophisticated and large-scale fraud. A 35-year-old Chinese national is alleged to have masterminded the entire scheme, creating a staggering 373,000 individual onion domains, or "micro-shops," on the Tor network. Each shop appeared as an independent marketplace, offering a menu of illicit goods and services, with a primary focus on advertising CSAM. The network also offered stolen credit card data and access to compromised computer systems.
However, investigators discovered the core business model was pure deception. An estimated 10,000 customers from around the globe were lured into making payments in cryptocurrency, primarily Bitcoin, for illegal content that was never delivered. This fraudulent model allowed the operator to amass over EUR 345,000 (approximately USD 400,000) between February 2020 and July 2025, preying on the criminal intentions of his customers while avoiding the complexities of actually trafficking the advertised materials.
Individually, these micro-shops were designed to be insignificant, flying under the radar of conventional cybercrime monitoring. Their sheer volume and fragmented nature created a digital smokescreen, making the network's true scale and centralized control nearly impossible to detect through traditional means. At its peak, the network's infrastructure relied on up to 287 servers, with a significant portion—105—located in Germany, which ultimately became a key focus for investigators.
The Digital Breadcrumbs: Cracking Anonymity
The turning point in the investigation came from CFLW Cyber Strategies and its proprietary Dark Web Monitor. Described by officials as a "search engine for the Darknet," the tool provided the crucial analytical lead that unraveled the network. Instead of looking at each micro-shop in isolation, analysts used the technology to identify subtle, repeating patterns across thousands of these seemingly unrelated sites.
The true innovation, however, was the correlation of this on-site data with cryptocurrency transaction patterns. By employing advanced analysis tools like GraphSense to trace the flow of Bitcoin payments from customers to the operator, investigators could definitively link the fragmented shops together. The digital money trail acted as an undeniable thread, weaving the thousands of disparate data points into a single, coherent picture of a massive, centrally controlled criminal enterprise.
This data-driven approach effectively pierced the veil of anonymity that the dark web and cryptocurrencies are designed to provide. It revealed that what appeared to be a decentralized ecosystem of minor criminal actors was, in fact, the work of one individual. The Bavarian Justice Minister, Georg Eisenreich, specifically praised the use of these "innovative tools" as instrumental in uncovering the operator and the full scope of his activities.
A Global Alliance Against Cybercrime
Operation Alice stands as a testament to the power of international cooperation. The complex investigation was a joint effort involving the ZCB, the Bavarian State Criminal Police Office (BLKA), the German Federal Criminal Police Office (BKA), and Europol, which played a central coordinating role. The collaboration extended globally, with law enforcement agencies from 23 different countries contributing to the effort.
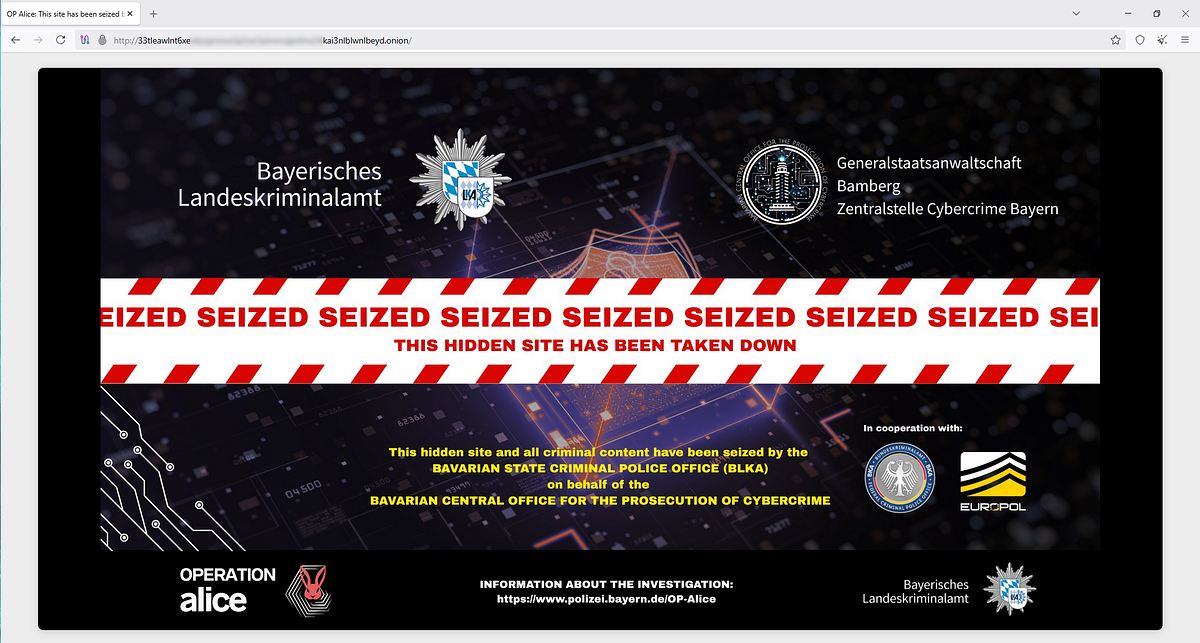
Europol facilitated the exchange of information and compiled investigative packages to be disseminated to the national authorities of the involved countries, ensuring a synchronized and effective global response. The successful takedown of the network, which now displays an official seizure banner across all its domains, brings the operation to a close.
The case is being widely compared to the landmark KidFlix investigation that concluded in April 2025, which also resulted in the removal of vast quantities of abusive material. Operation Alice, however, showcases a significant leap forward in technological capability, particularly in its ability to dismantle a fraudulent network by mapping financial transactions on a massive scale.
"We are pleased to have disrupted this extensive dark web network," said Thomas Goger, representing the Bavarian authorities. "The perpetrator played a central role in a major criminal infrastructure. Dismantling this network marks a significant step forward in several respects: applying cutting-edge law enforcement technologies, prosecuting about 600 offenders and users, and, most importantly, protecting potential future victims."
Targeting Demand: The Hunt for Users
Beyond dismantling the criminal infrastructure, Operation Alice has taken a firm stance against the demand that fuels such networks. Authorities have launched investigations into approximately 600 users worldwide who made cryptocurrency payments to the fraudulent shops. Even though they never received the illegal material, the act of attempting to purchase CSAM is a serious criminal offense in many jurisdictions.
To date, 440 of these individuals have been formally identified across the 23 participating countries, with over 100 facing active investigations. This focus on the user base sends a clear and powerful message: there is no anonymity for those who seek to acquire child abuse material online. Law enforcement now views these individuals not only as offenders but also as potential sources of intelligence for mapping broader criminal ecosystems.
The operation's success in identifying buyers demonstrates that financial transactions on the blockchain, once thought to be anonymous, can provide an indelible record for investigators armed with the right analytical tools. This strategic shift towards prosecuting the demand side is a critical component in the broader effort to make the internet a safer place and disrupt the vile market for child abuse. This comprehensive approach, combining technological innovation with global cooperation and a focus on both supply and demand, sets a new and formidable precedent in the ongoing war against dark web criminality.
