New Model Targets Healthcare's Static Cybersecurity Defenses
- 126% increase in ransomware attacks on healthcare from 2023 to 2024
- $9.7 million average cost of a healthcare data breach (highest across industries)
- Posture 1 ('Structured but Static') is the most common security maturity level among early adopters of HC-ZTMM™
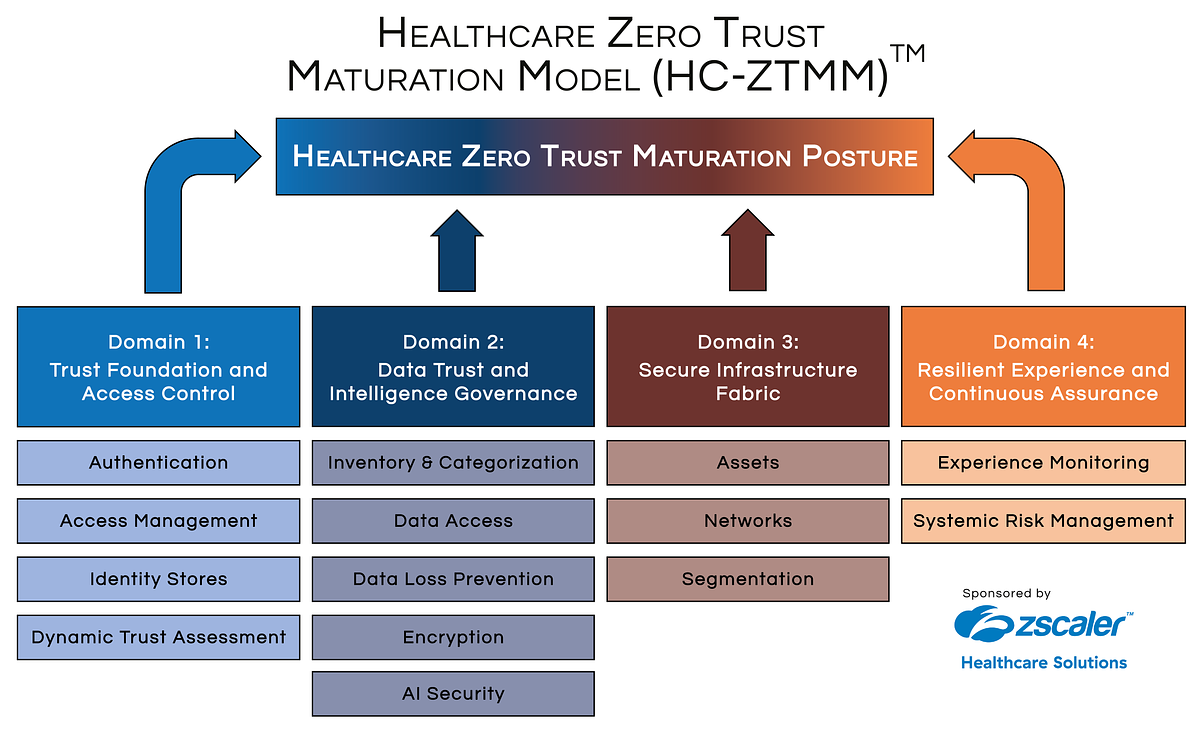
Experts agree that the Healthcare Zero Trust Maturation Model (HC-ZTMM™) represents a critical step forward in addressing healthcare's cybersecurity challenges by providing a clinically informed, dynamic framework tailored to the sector's unique needs.
New Model Targets Healthcare's Static Cybersecurity Defenses
NASHVILLE, TN – February 23, 2026 – As the healthcare industry grapples with an unprecedented wave of cyberattacks, a new framework launched today at the ViVE26 conference aims to shift the sector’s defensive posture from static and reactive to dynamic and clinically aware. The Alliance for Smart Healthcare Excellence, in collaboration with industry partners including cybersecurity firm Zscaler, has officially released the Healthcare Zero Trust Maturation Model (HC-ZTMM™), the first assessment tool of its kind designed specifically for the unique operational and patient-safety demands of clinical environments.
The model provides a structured, data-driven method for healthcare providers to assess and benchmark their "Zero Trust" security maturity. Offered free of charge to qualified organizations, the HC-ZTMM™ promises to move beyond generic security checklists, offering a path toward a more resilient and intelligent defense system that protects patient data without hindering the delivery of care.
A Sector Under Digital Siege
The launch of the HC-ZTMM™ comes at a moment of critical need. The healthcare sector is facing a cybersecurity crisis, with a 126% increase in ransomware attacks from 2023 to 2024. These attacks are no longer mere data heists; they are direct threats to patient safety, capable of shutting down hospital operations, delaying critical procedures, and corrupting patient records. The financial toll is staggering, with the average cost of a healthcare data breach now exceeding $9.7 million, far surpassing any other industry.
While legacy frameworks like the NIST Cybersecurity Framework provide foundational guidance, the rapid digitization of healthcare—fueled by telehealth, AI-driven diagnostics, and a sprawling Internet of Medical Things (IoMT)—has introduced vulnerabilities that generic models struggle to address. Outdated medical devices running unsupported software, fragmented network monitoring, and the sheer volume of interconnected systems create a vast and porous attack surface. Cybercriminals are increasingly exploiting these gaps, often through third-party vendors or sophisticated phishing campaigns, turning trusted connections into attack vectors.
"Healthcare is at a critical inflection point," said Steve Lieber, Executive Chairman of the Alliance for Smart Healthcare Excellence, in the announcement. "Digital health, AI, and expanded data exchange are accelerating faster than most security operating models can adapt. HC-ZTMM™ exists because healthcare leaders need an objective, clinically grounded assessment that shows not just whether Zero Trust controls exist, but how well they work together under real clinical conditions, right now, not someday."
Beyond the Checklist: A Clinically-Informed Approach
The core innovation of the HC-ZTMM™ is its explicit focus on the clinical environment. Traditional Zero Trust architecture—which operates on the principle of "never trust, always verify"—can be challenging to implement in a hospital setting where seconds count and clinician access must be swift and seamless. Coarse access roles and cumbersome multi-factor authentication (MFA) prompts can impede care, leading staff to create manual workarounds that inadvertently re-open security holes.
The HC-ZTMM™ was designed to overcome this conflict. Developed through a multi-stakeholder process involving health system security executives, the model evaluates maturity not just on the presence of security controls, but on their integration with clinical workflows. It accounts for healthcare-specific challenges such as the proliferation of non-human identities (like medical devices and automated systems) and the non-negotiable priority of patient safety.
"From the outset, the goal was rigor and practicality," noted Frank Nydam, Executive Director of Healthcare Strategy at Zscaler, a key collaborator on the project. "The assessment development process brought together security architecture expertise with frontline healthcare perspectives. That combination is what makes HC-ZTMM™ so robust, it evaluates maturity across identity, data, infrastructure, and experience using real-world signals, not theoretical ideals." The goal is to create a security posture where Zero Trust policies operate invisibly in the background, securing every connection without adding friction for a clinician accessing an EHR or a surgeon relying on a connected device.
The 'Structured but Static' Problem
Early findings from the initial cohort of organizations that used the HC-ZTMM™ reveal a widespread and dangerous vulnerability: most are stuck at what the model defines as Posture 1, "Structured but Static." This means that while foundational security controls like firewalls and basic access policies are in place, they lack the continuous, automated, and cross-domain enforcement needed to thwart modern cyber threats.
This static posture creates significant blind spots. One of the most critical findings is the lack of dynamic trust assessment. In a Posture 1 environment, a user's or device's identity and permissions are typically verified only once at the point of login. After that initial check, they are often granted broad access, allowing a potential intruder who compromises an account to move laterally across the network undetected. A dynamic, continuous model, by contrast, would constantly re-evaluate trust based on context, such as user behavior, location, and the data being accessed, revoking permissions instantly if suspicious activity is detected.
The persistence of this static state is often a direct result of prioritizing clinical usability over security hardening. Organizations have historically opted for selective MFA adoption and overly broad access roles to avoid disrupting care delivery. While well-intentioned, this approach leaves critical systems and sensitive patient data exposed. The HC-ZTMM™ provides a roadmap for organizations to mature beyond this state, helping them implement stronger, more dynamic controls that are intelligently tailored to the clinical context, thereby enhancing both security and patient safety.
A Collaborative Path to Cyber Resilience
The HC-ZTMM™ represents more than just a new tool; it signifies a collaborative industry effort to establish a higher standard for cybersecurity in healthcare. By offering the assessment for free, the Alliance for Smart Healthcare Excellence is lowering the barrier to entry, enabling health systems of all sizes to gain a clear, objective baseline of their current posture and benchmark themselves against their peers.
This data-driven insight is crucial for prioritizing investments. Instead of making scattershot security upgrades, organizations can use the assessment results to target their weakest areas and build a strategic roadmap toward a more mature, intelligence-driven Zero Trust architecture. The model's framework is designed to help bridge the common divide between IT security departments and clinical engineering teams, creating a shared language and set of goals centered on protecting the organization while enabling its core mission of patient care.
The involvement of industry leaders like Zscaler lends significant technical weight to the model, ensuring its principles are grounded in proven security architecture. This synergy between a non-profit thought-leadership organization and a leading technology vendor points toward a future where security standards are co-developed and aligned with real-world needs. As healthcare becomes increasingly digital and interconnected, frameworks like the HC-ZTMM™ will be essential for building the resilience needed to protect patient data, maintain operational continuity, and secure the trust upon which the entire healthcare system is built.
