Enigma Networks' SOC 2 Signals Shift to Internal Network Defense
- Average 'breakout time' for attackers: 29 minutes (2025 data, per CrowdStrike)
- Cost of AI-powered data breaches: $5.72 million (2025 average)
- Malware-free attacks: 82% of all attacks
Experts agree that the cybersecurity landscape is shifting from perimeter defense to internal network governance, with SOC 2 compliance serving as a critical benchmark for vendor trust.
Enigma Networks' SOC 2 Signals Shift to Internal Network Defense
PHILADELPHIA, PA – April 29, 2026 – Enigma Networks, a company championing a new category of cybersecurity called Zero Trust for Internal Networks (ZTNX), today announced it has completed its SOC 2 Type I examination. The successful independent audit attests to the design of the company's security controls, providing a formal credential at a time when the very nature of cyber threats is forcing a strategic shift in enterprise defense, moving focus from the perimeter to the chaotic, often-unguarded landscape of internal networks.
The announcement comes as security leaders grapple with an uncomfortable truth: breaches are inevitable. The new battleground is no longer just the digital wall of the castle but the corridors within it. AI-driven attacks are compressing the timeline from initial compromise to widespread internal damage from days or hours to mere minutes, making the governance of internal network trust a board-level concern.
The New Battleground: Inside the Network
For years, cybersecurity followed a castle-and-moat philosophy: build strong perimeter defenses to keep attackers out. However, once that perimeter is breached—through a phishing email, a compromised credential, or a vulnerable application—attackers often find themselves in an environment of implicit trust. Systems, servers, and devices are frequently allowed to communicate with each other with minimal scrutiny, a vulnerability attackers exploit for lateral movement.
Recent industry data paints a chilling picture of this new reality. According to cybersecurity firm CrowdStrike, the average 'breakout time'—the time it takes for an attacker to move laterally from an initially compromised host to another system within the network—shrank to just 29 minutes in 2025, with the fastest adversaries clocked at a blistering 27 seconds. This acceleration is largely fueled by AI, which automates reconnaissance, credential theft, and intrusion steps. Furthermore, an astonishing 82% of attacks are now malware-free, leveraging legitimate tools and trusted internal pathways to evade traditional detection, making them appear as normal network activity.
"As enterprises confront the reality that breaches are inevitable, the focus is shifting from prevention alone to containment and control," said Bob Moul, CEO of Enigma Networks, in the company's announcement. "That requires governing internal trust, not just at the perimeter or point of access."
This shift is critical. The financial impact of failing to control internal threats is staggering. Recent studies show the average cost of an AI-powered data breach hit $5.72 million in 2025. Breaches involving unsanctioned 'Shadow AI' tools within an organization added an average of $670,000 to that cost, highlighting the danger of ungoverned internal systems.
A Stamp of Approval: What SOC 2 Means for Security
In a market saturated with security solutions, verifiable trust is a vendor's most valuable currency. Enigma Networks' completion of the SOC 2 Type I examination serves as a foundational step in building that trust with enterprise customers. Developed by the American Institute of Certified Public Accountants (AICPA), SOC 2 is a rigorous compliance standard that defines how organizations should manage customer data across five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
A Type I report, specifically, assesses the design of a company's security controls at a single point in time. An independent third-party auditor has verified that Enigma Networks has designed and implemented the necessary security processes and controls to protect customer data. For enterprises entrusting a vendor with visibility into their most sensitive internal communications, this audit provides a critical, baseline level of assurance.
While a Type I report is a 'snapshot' in time, it is a crucial milestone, especially for a company in an emerging category. It demonstrates a formal commitment to security and can significantly shorten sales cycles with large enterprises that have stringent vendor compliance requirements. Enigma Networks has also stated it is pursuing its SOC 2 Type II examination, a move that signals a deeper commitment. A Type II report goes further by auditing the operational effectiveness of those controls over an extended period (typically 3-12 months), providing customers with even greater confidence in a vendor's long-term security posture.
Governing Trust in an Untrusted World
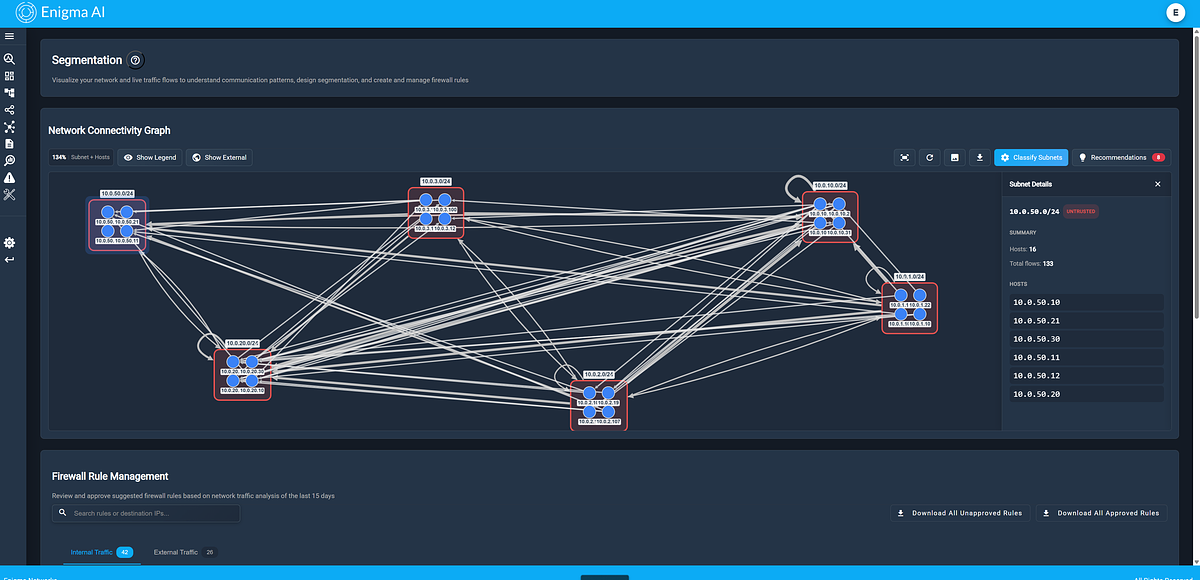
Enigma Networks aims to solve the internal threat problem with its Enigma AI platform, which is purpose-built to deliver what the company calls 'Internal Trust Governance.' The platform addresses the gap left by traditional Zero Trust architectures, which have historically focused on user identity and access control at the network edge.
“Enterprise security teams are trusting Enigma AI with visibility into their most sensitive internal communications – the lateral traffic between assets, AI models, and infrastructure that no one else governs,” stated Mark Viglione, Co-founder and CTO of Enigma Networks. “SOC 2 Type I is our formal commitment that we hold ourselves to the same standards we ask of the networks we protect.”
The core function of Enigma AI is to continuously analyze the web of internal communications across IT, OT, IoT, and cloud environments to determine which connections are necessary, expected, and safe. By using machine learning to establish a baseline of normal operational behavior, the platform can then generate granular microsegmentation policies. These policies enforce a principle of least privilege, ensuring that workloads and systems can only communicate in explicitly authorized ways.
This process is designed to surface what the company calls 'trust drift'—subtle deviations from the established baseline that could indicate a compromise or misconfiguration before it escalates into a full-blown breach. By spotting an unusual connection between a marketing server and a database of financial records, for example, the system can raise an alert or automatically block the communication, effectively neutralizing threats at machine speed.
Investor Confidence and Market Trajectory
The strategic importance of securing internal networks is not lost on the investment community. Enigma Networks is backed by early-stage investors including Osage Venture Partners, a firm with a track record of investing in disruptive B2B software and cybersecurity innovators. This backing provides not only capital but also a vote of confidence in the company's vision and its approach to a complex and growing market need.
The industry is clearly at an inflection point. The rise of AI as both a tool for attackers and a target for attack, combined with the increasing complexity of hybrid cloud and IoT environments, has rendered perimeter-only security models obsolete. The focus is now shifting inward, toward gaining visibility and control over the east-west traffic that has long been a blind spot for security teams. Enigma Networks' recent compliance milestone and its focus on this emerging frontier place it squarely at the center of this crucial evolution in enterprise cybersecurity.
📝 This article is still being updated
Are you a relevant expert who could contribute your opinion or insights to this article? We'd love to hear from you. We will give you full credit for your contribution.
Contribute Your Expertise →